
Modern Threats requires Modern Solutions
Modern threats require modern tools and expert skills on how to utilize them.
2020 and 2021 have been challenging years for all of us. Covid-19 has changed the gameplay forcing users to be productive while working from home while still maintaining security. We know that the threat landscape is continues to evolve and the attacks them self are even more complex where the attackers exploit a vulnerability in the target systems to gain foothold to then lateraly move to their end goal, the most critical information and highest value assets. But what we can see now is that the attacks are even more sophisticated and the level of finesse of these attacks are also increasing.
This leads to one of many conclusions:
The era when one could protect individual areas such as identities, information or devices to stay safe is over!
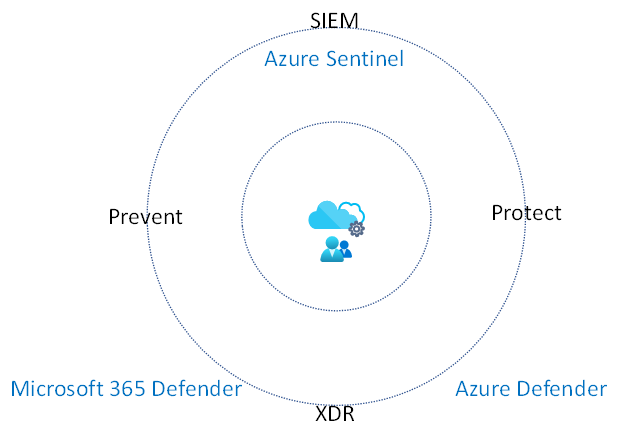
The new path is Extended Detection and Response (XDR) which is designed to deliver intelligent, automated and integrated security across Identities, Endpoints, Email, Documents and Cloud applications. What is needed is a way to see end to end threats across all assets along with all signals and alerts correlated to incidents which are prioritized based on threat intel, AI and Machine Learning. On top of this one should have the possibility to have coordinated actions across the organization. In short sentence, XDR capabilities together with a Security Information and Event Management (SIEM) with Security, Orchestration, Automation, Response (SOAR) capabilities.
Microsoft delivers both:
XDR through the Microsoft 365 Defender and Azure Defender which gives prevention, detection and response to threats across Identities, Endpoints, Email, Documents and Cloud applications, IoT, on-premises and Cloud infrastructure.
SIEM with SOAR through the cloud-native Azure Sentinel to which you easily can connect your Defender products along with your other security solutions such as firewalls and other third-party network equipment, web services logs and other systems logs.
Microsoft's XDR and SIEM combination gives the defenders yet another advantage by using Azure Sentinel to get a collective view and then utilize Microsoft 365
Defender to drill down in an incident to get further information. Incidents, schema and alerts are shared between the products and the information flow is bi-directional.
Onevinn’s MDR service is leveraging from these XDR and SIEM solutions along with our security expertise, threat intelligence skill along with our deep partnership with Microsoft. Onevinn’s MDR service is 24/7/365 service to help you to stay ahead of the attackers.
One of our main goals is to have as early detection, prevention and response as possible. This means decrease the time from detection to response but also the prevention. Onevinn achieves this by leveraging Microsoft XDR and SIEM solution together with their expertise.
Onevinn’s MDR differs from the traditional SOC by acting in our customers environments instead of just giving our customers a heads up. Our MDR analysts are investigating incoming incidents by doing a triage to take the proper immediate action to remediate the threat by for example resetting a user’s password, isolating a device or start a deeper investigation with a Cyber Security Expert.
Along with this, Onevinn has a Digital Forensic Incident Response (DFIR) team helps our customer in the case of a major security incident.
If you want learn more about our MDR service, please read here or watch this webinar!


