
Why we created Security Testing.
Why did we create Security Testing?
Offensive security tests are a vital part of improving an organizations overall security posture. These types of procedures help organizations to identify where they are the most likely to face an attack and proactively remediate these weaknesses prior to any exploitation by real threat actors. Listed services should not be limited to a one-time effort but should rather be seen as ongoing security developments.
What does Onevinn’s Security Testing encompass?
With our certified offensive security specialists, we provide a solid understanding of both the exploitation processes and the hacker mindset, ensuring a quality foundation that has been incorporated into a wide range of offensive security testing solutions – ranging from application security testing to full scale adversary scenario simulation.
Some services we currently offer are the following:
- Penetration tests
- Red Team engagements
- Offensive security Training & Education
- Vulnerability Assessments and Scanning
- Purple Team
All these services help organizations identify and remediate vulnerabilities and security oversights in unique and critical ways.
Penetration testing
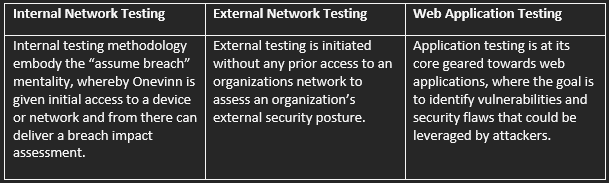
Onevinn’s penetration tests offer systematic security evaluations focused on systems, networks, or applications, where the goal is to identify weaknesses to further develop an organisations security posture.
Some examples:
 Red Team
Red Team
Red Teaming is the simulation of a known threat targeting an organization through characteristic means, thereby establishing the effectiveness of the processes, technology and people utilized in protecting the organisation.
Training & Education
Onevinn’s education solutions provide offensive security courses and awareness training for schools and companies alike.
Vulnerability Assessment/Scanning
The Vulnerability Assessment solution utilizes vulnerability assessment tools to identify, evaluate, and report on security vulnerabilities within your networks, applications, or systems.
How do I know which service is suitable for my organization?
To understand, when discussing the applicability of each security testing service, a correlation to the cyber maturity model is key for receiving applicable actions from these services. This is of course something we discuss upon initial contact.
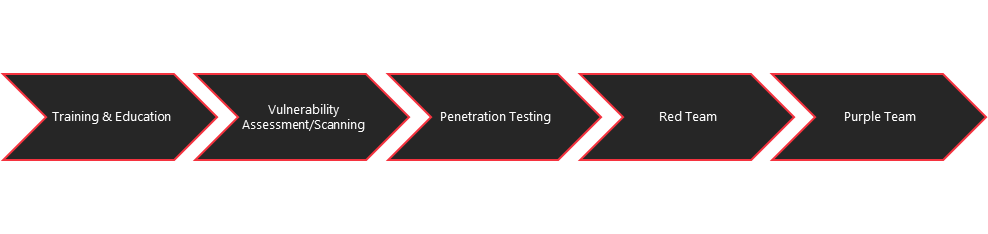 We can visualize our cyber maturity as building blocks of progressing security improvements. An organization’s maturity in one block will be a determining factor for what service would increase their security posture.
We can visualize our cyber maturity as building blocks of progressing security improvements. An organization’s maturity in one block will be a determining factor for what service would increase their security posture.
For example – a hypothetical organization which lacks a blue team will not benefit for the full deliverables of a red team engagement. This is because a sizable aspect of a red team engagement includes the testing of an organization’s detection and response capabilities, after which the lacking aspects of these capabilities are discussed and improved upon.
Therefore, the ideal red team delivery is towards an organization that has conducted pre-emptive security work – such as establishing an SOC – and want to identify organizational oversights and weaknesses through the simulated attack on an infrastructure by a sophisticated threat actor.
In conclusion – an organization without established security procedures will likely gain more from a vulnerability scan or assessment than a red team engagement.
Penetration tests and Vulnerability discovery focused assessments are also a great way of limiting scope to an application or network segments, making these services the perfect option for a more targeted engagement.
If you want to know more: Sign up for our webinar on Wednesday using this link below:
Security Testing Webinar
And more info can be view at: Onevinn Security Testing

